
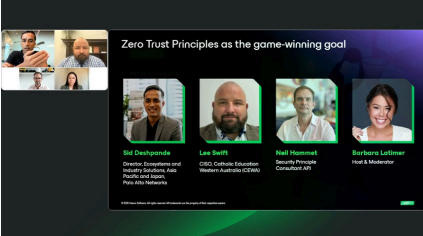
Zero Trust Principles as the GameWinning Goal Against Ransomware
Trust no one, verify everything—that’s the foundation of zero
trust security. With remote work and multi-cloud services
gaining traction—cyberattacks are more advanced than ever,
and relying on outdated security measures is a losing strategy.
Organizations need an approach that adapts to threats in real
time.
Zero trust changes the game by eliminating blind trust in any
user, device, or network.
How can companies successfully adopt zero trust? Join
industry experts as they explore:
- The key principles of zero trust and why it matters now more than ever
- How organizations are adopting zero trust and what the data tells us
- Pitfalls to avoid in zero trust implementation
- Real-world adoption trends and industry statistics
- How does relying on cybersecurity specialists like Veeam
- Ransomware help organizations in building a zero trust
framework?
Register to Download